VPN
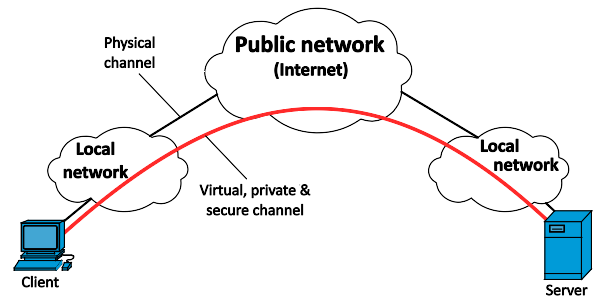
VPN (Virtual Private Network) is a connection between two computers or other endpoints in which packets sent over a shared network, for example, the Internet, are automatically encrypted and decrypted by the endpoints. Although the packets are carried on a shared network, their contents are protected from unauthorized access between the endpoints. Virtual private networks are commonly used to connect branch offices to a headquarters when the cost of a physically separate communications link cannot be justified, or to allow workers to access their company network across the Internet when they are not on the premises.
There are many VPN products, to better understand them first need get to know VPN protocols.
IPsec
IPsec (Internet Protocol Security) is a secure network protocol suite that authenticates and encrypts the packets of data to provide secure encrypted communication between two computers over an IP network.
L2TP
L2TP (Layer 2 Tunneling Protocol) is a tunneling protocol used to support virtual private networks (VPNs). It does not provide any encryption or confidentiality by itself. IPsec is often used to secure L2TP packets by providing confidentiality, authentication and integrity. The combination of these two protocols is generally known as L2TP/IPsec. It is standardized in RFC 3193.
L2TP use UDP as transport layer.
L2TPv3
L2TPv3 defines the base control protocol and encapsulation for tunneling multiple Layer 2 connections between two IP nodes.
It is standardized in RFC 3931.
PPTP
obsoleted, do NOT use.
IKEv2
- Improvements to support for NAT traversal and firewall traversal in general.
- Standard Mobility support: There is a standard extension for IKEv2 (named MOBIKE) used to support mobility and multihoming for it and Encapsulating Security Payload (ESP). By use of this extension IKEv2 and IPsec can be used by mobile and multihomed users.
- highly reliable when switching between internet connections, like from mobile network to WiFi network.
IKEv2 is standardized in RFC 7296.